Both your Subscriber Identity Module (SIM) card and your mobile phone itself can identify who you are. Any communication your phone has with the mobile network – whether placing or receiving a call, sending a message, browsing the web or just remaining connected – includes identifying information about the phone and the SIM card.
For further security practice, walk through the Security in-a-Box basic security setup for Android devices.
How Can a SIM Card Compromise Me?
The SIM card stores information about the mobile service subscriber. It is what your service provider uses to identify who you are, based on personal information or documents that you submitted.
How Can My Mobile Phone Compromise Me?
A SIM card identifies you, but your mobile phone can get you into trouble. Each mobile phone has a unique number, the International Mobile Equipment Identity (IMEI). This number can be tracked at all times.
Check your mobile phone for the IMEI (often located behind the battery) or dial *#06# from your phone to find out your mobile phone’s unique number.
You may assume your SIM card is the only way for a mobile service provider or authorities to identify you or track your location. Many people change their SIM cards frequently, but continue to use the same phone. This is a mistake! The combination of your SIM card (which identifies you) and IMEI number (which identifies your phone) allows you to be identified and tracked constantly.
Your mobile phone constantly registers your location on every cell tower it connects to. Take out your battery or leave your phone at home if you do not want to be tracked.
How Does My Phone Show My Location?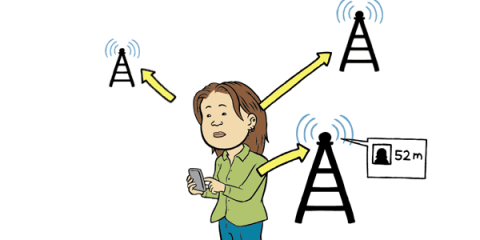
When your mobile phone is switched on, the network knows your location, triangulated from the cell towers nearby that record your phone’s signal. Your location might be accurate within a few metres in a densely populated area but only to a few hundred metres in a rural area with few cell towers. If you make or receive a call or text message, your location at that time is stored in network records.
Note that this is a function of the mobile network, not surveillance. All networks triangulate your signal. This is important to remember as this information can be used against you!
Can My Phone Be Used to Eavesdrop on Me?

Even when you are not using your mobile phone, it can be used as a secret microphone for others to listen to you. Take out your battery (do not just turn the phone off ) or keep your phone far away while having private conversations.
In normal use, your text messages and phone calls can be monitored by your network operator. Calls can be listened in to and recorded, and recordings can be passed (legally or illegally) to someone else.
A few Things to Remember to Help You Stay Safer:
- Buy prepaid SIM cards, and if at all possible avoid registering the SIM in your name.
- Buy a cheap, low-tech mobile phone that you do not mind throwing away if necessary.
- If you are concerned about being monitored, do not just change your SIM card, get rid of your mobile phone too.
- Always try to avoid sharing sensitive information over your mobile phone.
Things to Remember
- Your SIM card and your mobile phone can identify you.
- Your mobile phone can track you.
- Your mobile phone can eavesdrop on you.
- Carry extra SIM cards from other mobile network operators that you can switch with your regular SIM. If possible, carry more than one phone.
- Take your battery out of your phone during and when travelling to and from group meetings to avoid cell phone triangulation and location tracking.
- If you are concerned that you are being tracked by authorities, get rid of both the SIM card and the phone that you have been using.
- Airplane mode is not a failsafe option to avoid tracking, your phone may still enable the manufacturer to access it via a backdoor.
As a citizen journalist, you’ll likely be using your mobile phone for much more than just shooting and sharing video. Because you’ll likely be using a browser or mobile data at some point, be sure to check out the following StoryMaker security lessons:
2.9: How can I use a browser safely?
2.10: How can I manage mobile data safely?
It is HIGHLY recommended that you complete all of the security lessons in the StoryMaker app, especially if you answered yes to the questions listed above. Other lessons include:
2.3: How do my communications put me at risk?
2.5: What makes a strong password?
2.6: How do I effectively use pseudonyms?
2.7: How can I use SMS safely?
2.8: How can I send email safely?